Cybersecurity is everyone’s responsibility. Staying vigilant against potential hackers and scammers will help to keep our campus safe. The following is a quick summary of the most likely scams you will encounter, how to recognize them, and what to do when you spot them.
Common Types of Attacks
Phishing
Phishing is when the scammer sends you an email to try to trick you into sending them sensitive information like passwords or account numbers, or to download malicious software. A lot of times they will pose as a coworker or a company we do business with (like Microsoft or Adobe) and send what looks like a legitimate email with a link that goes to a site where you’re supposed to type in your username and password.
Tech Support Phishing Scam
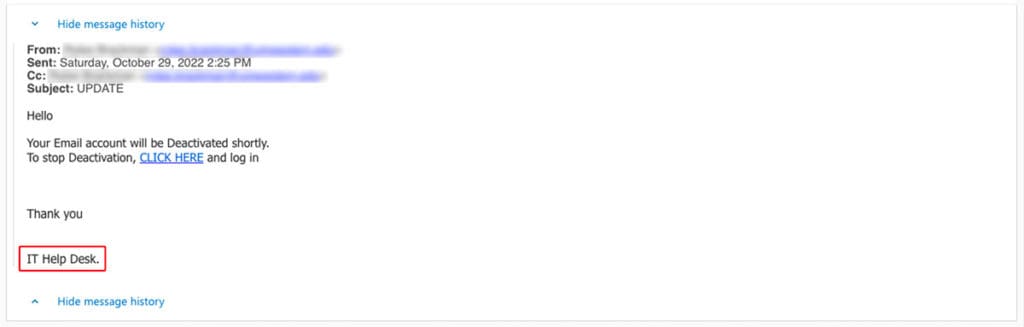
Scammers will contact you posing as Tech Support (think “Microsoft Tech Support” or “IT Help Desk”). They will say there is something wrong with your computer or your account and have a link for you to click. Below is a real example below of a phishing attempt on someone at UMW. Notice “IT Help Desk” circled in red. Someone is trying to pose as IT to get the victim to click that link.
How to Spot a Phishing Attempt
Unexpected Email
Getting an unsolicited email out of the blue from someone you never do business with. When this happens, take a moment to look for the other signs on this list.
Suspicious Email Address
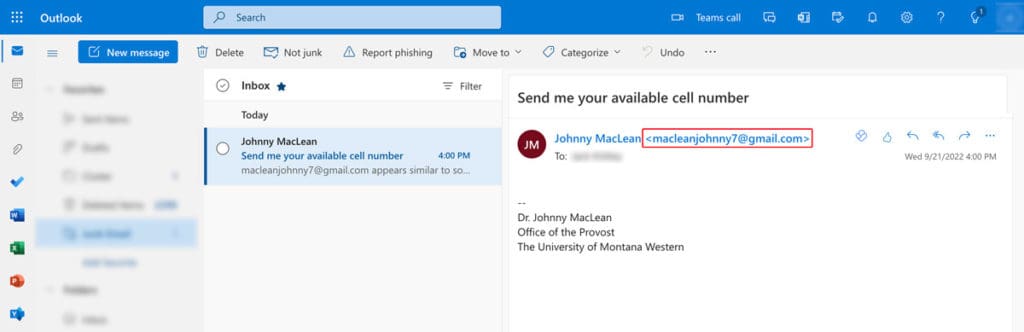
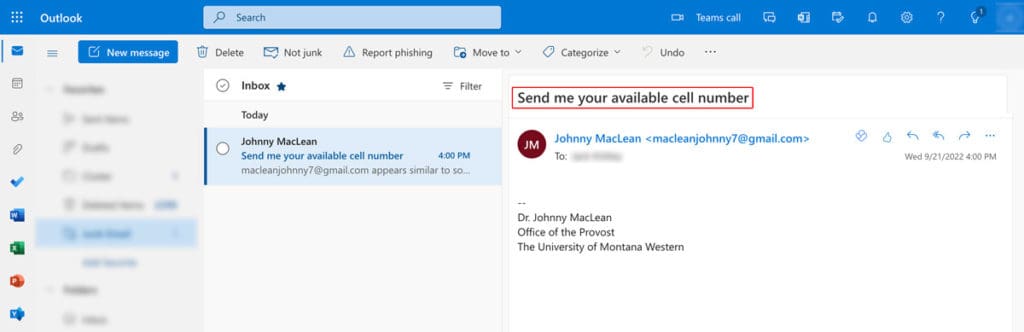
The sender’s name makes it seem like someone from the university is emailing you but their email address is from gmail or another site that seems suspect. See example below and the email address circled in red. If someone from the University is emailing you, they will be using their @umwestern.edu email account, not a gmail account that could really be owned by anybody.
Links to Sites that Look Legit at First
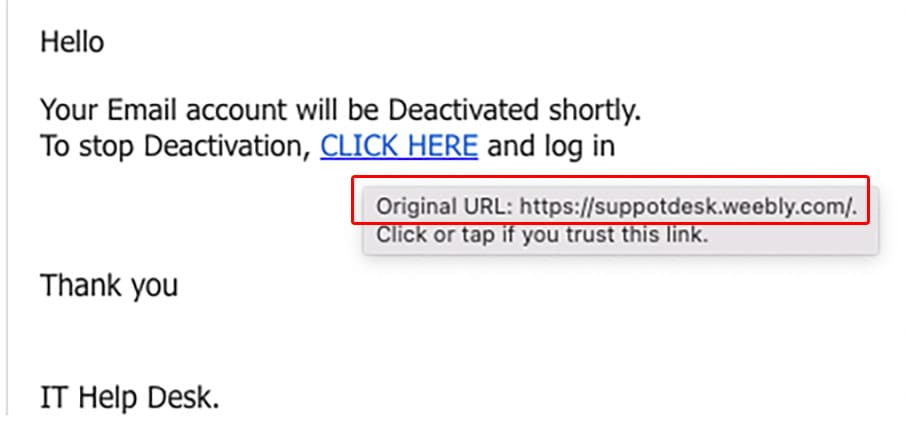
In the “IT Help Desk” example above, a link (circled in red) was sent to a student saying, “CLICK HERE”.
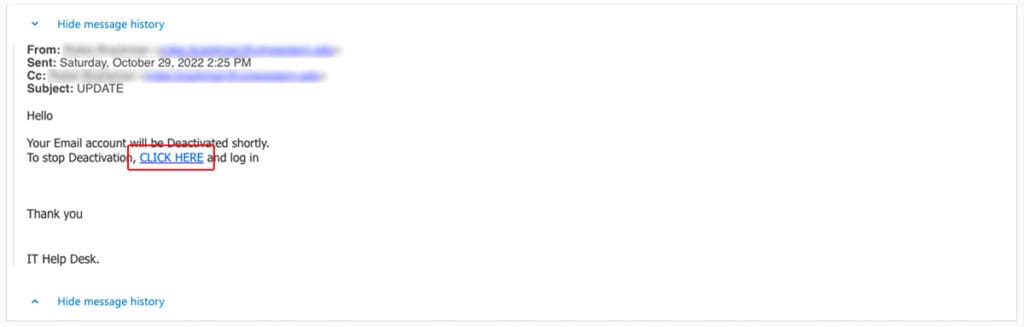
But if you hover your mouse over the link WITHOUT CLICKING IT, you can preview the address the link goes to and see it goes to a shady site that has nothing to do with UMW:
Spelling and Grammatical Errors
Oftentimes the scammer is not a native English speaker and their odd spelling or grammar (circled in red in the real example below) gives them away:
Urgency
The message pressures you to act now like in the example of the Tech Support Phishing Scam above.
What to Do if You Get a Suspicious Email
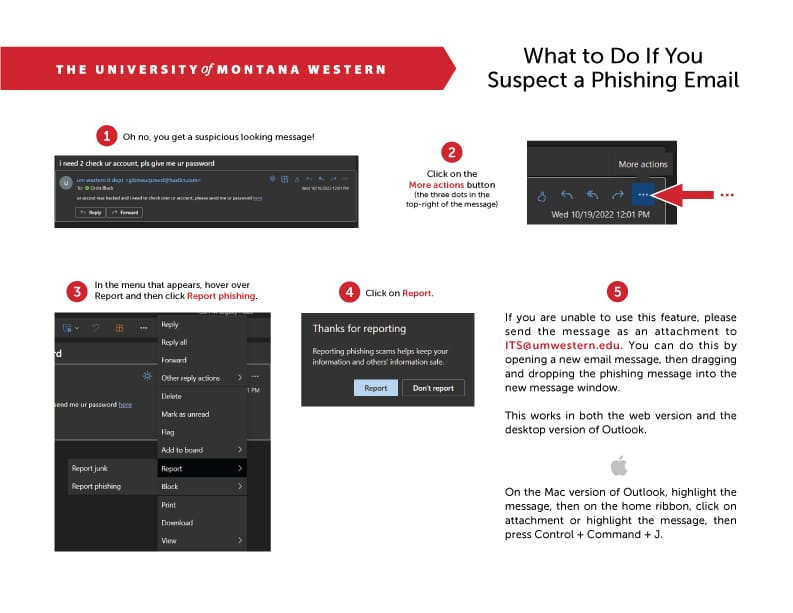
Immediately report any suspicious email to the IT department. Here’s a printable pdf that explains how to report in your umwestern.edu email account:
If you’re just not sure if something is a scam or not, reach out to our capable IT department!
Reach us through the form on this page:
By phone:
(406) 683-7777
Or by email:
For more information, see the Federal Trade Commission’s Page on Phishing.
